Disclaimer: The original of this page written in Dutch. This page has been automatically translated into other languages using DeepL. This may result in differences in nuance, tone and meaning. When in doubt, always consult the Dutch version first. Due to the high cost of translations, this page may lag behind the Dutch version in terms of content. We consider the Dutch version of this page to be leading.
0: Summary
Your organization received an e-mail on Feb. 9 or 10 about becoming transparent about government online security. This e-mail came from the Internet Cleanup Foundation and was sent to all regional governments and CERT / CISRT organizations of all European member states.
Starting May 10, your organization’s online security will become public on the SecurityBaseline.eu website. From February 10 through May 10, this website will be available via the direct link in the email received. Measurement results can be viewed that way so any improvements can still be made before publication. We measure your online safety daily to weekly so that improvements can also be seen. We continue to measure, even after publication.
The measured services and published information are carefully considered and do not add new risks to your online environments. Our approach makes your environments more transparent, making them more manageable and therefore more secure. We do this on our own initiative, from a non-profit foundation, in our spare time. As European citizens, we are intrinsically motivated to play our part in creating a secure, sovereign and privacy-friendly online Europe and have extensive experience in doing so.
The Measure Europe initiative replicates our approach to measuring the online security of key organizations in the Netherlands. We started this in 2016. This has been so successful and practical that our website and activities have been included in policy documents of the Dutch Ministry of Security and Justice and the Dutch Ministry of the Interior and Kingdom Relations.
With the increasing digitization of governments and the recently increased pressure on sovereignty of online governments, we decided to start measuring all governments in Europe. We measure governments first sector by country because they are able to set guidelines and laws for themselves and for others.
Extensive background information about us and this initiative is on this page. The Internet Cleanup Foundation wishes everyone a safe online Europe.
Elger Jonker, Johan Bloemberg, Wouter Goyen
Table of contents
- What will happen
- Case study: the Netherlands measured since 2016
- Timeline of perusal, publication and scope
- Policies of the Internet Cleanup Foundation
- Accessibility
- How did the maps and announcements come about
- Financial Overview
1: What will happen
As of May 10, your organization’s basic online security is published at https://securitybaseline.eu. The published information may contain vulnerabilities in your online infrastructure but does not increase existing risk. Until publication, you can access your vulnerabilities through the links you received in that e-mail.
There are three months between February 10 and May 10. We call these three months the run-up period. This period is consistent with the time frame that is common within the “Coordinated Vulnerability Disclosure” guidelines of several European member states. In principle, everything we measure and publish is already public information. Thus, we are not using this period to comply with the Coordinated Vulnerability Disclosure process, but to make use of the existing routes and processes within the European member states that have been built to strengthen information security.
On our website, you will see maps of different layers of your government. On these maps, security is indicated by the color of a traffic light: red, orange and green. Green means everything is in order and red means one or more vulnerabilities are present. Orange requires action but less quickly than red. The example case of the Netherlands, further down this page, shows how the Netherlands is doing. This map is already public, because it has been public information for many years.
We are aware that our approach may raise questions or not be immediately perceived as pleasant or valuable. We are also aware that cultures vary greatly between different European countries. Our goal is to make a more resilient online Europe. Transparency is an appropriate means to that end. We assume that the government wants to protect European citizens well. This should translate into high quality online services. It is precisely this that is independently measurable and verifiable: that is what we offer.
2: Case study: the Netherlands measured since 2016
We started measuring the main websites of Dutch municipalities in 2016. This has expanded over the years to all websites of all Dutch governments. We also perform the same measurements on all Dutch educational institutions, healthcare and critical infrastructure. This data is public for everyone. It involves about 330,000 addresses of 10,000 organizations measured in 25 conclusions. This information can be viewed by anyone.
In the Netherlands, our initiative has led to hundreds of thousands of information security improvements. By using leading measurements, from internet.nl and our own privacy measurements, among others, we have been helping the country we live in become and remain secure for years.
This success is also the reason why the Netherlands is the only country already publicly visible on SecurityBaseline.eu: in fact, almost all organizations already score green, where in the same scope and measurements almost all other European government organizations still score insufficiently secure. So the Netherlands is already many years ahead of the rest of Europe. This is not only because of us, but also because of the adoption and steering of standards by the government and having legislation for encryption, for example.
The Dutch government has an open culture. This culture is also enshrined in legislation through the“Open Government Act“: every citizen is therefore entitled to access public information without having to meet any conditions. The Dutch government therefore wants to be transparent and is therefore approachable. The government dares to indicate where improvements are needed, which is why our initiative to measure the Dutch government has also been well received.
Our website and activities appear in policy documents of the Dutch Ministry of Security and Justice and the Ministry of the Interior and Kingdom Relations.
In the Netherlands, we also conduct all kinds of research. For example, we have made the following discoveries, the articles are in Dutch:
- Dutch government misses many thousands of sites in its overviews (2025)
- Government asks permission to track visitors in 100 different ways (2024)
- 4% of government sites post unsolicited tracking cookies to track visitors (2023)
- 33% of government sites do not comply with law to implement proper encryption on websites (2023)
- 7% of mail to the Dutch government goes through non-European parties (2024)
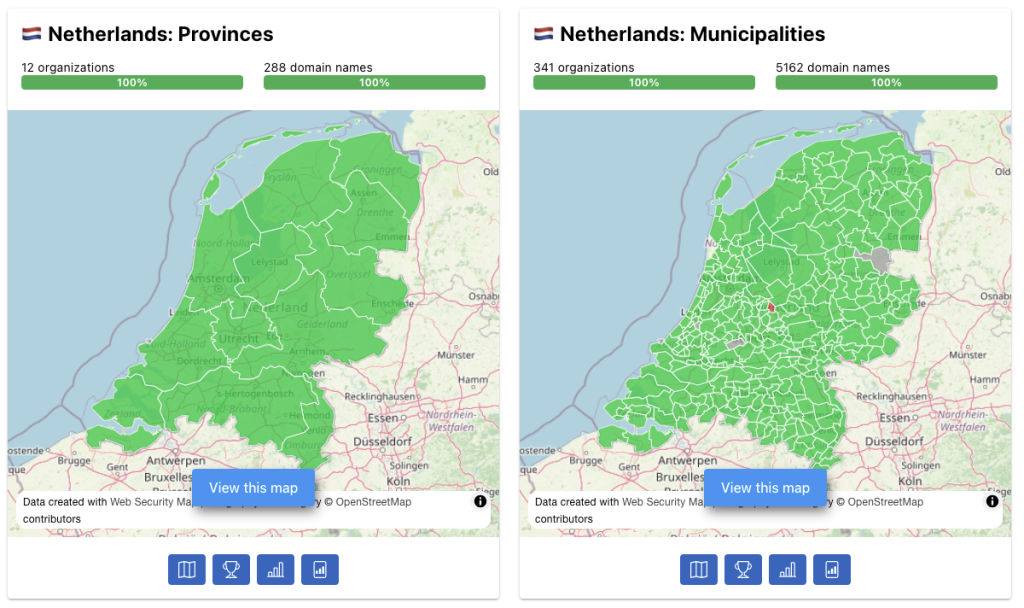
The screenshots below show an interim version of the maps of Dutch provinces and municipalities. This was pulled from SecurityBaseline.eu and is already publicly viewable because almost everything is in order.
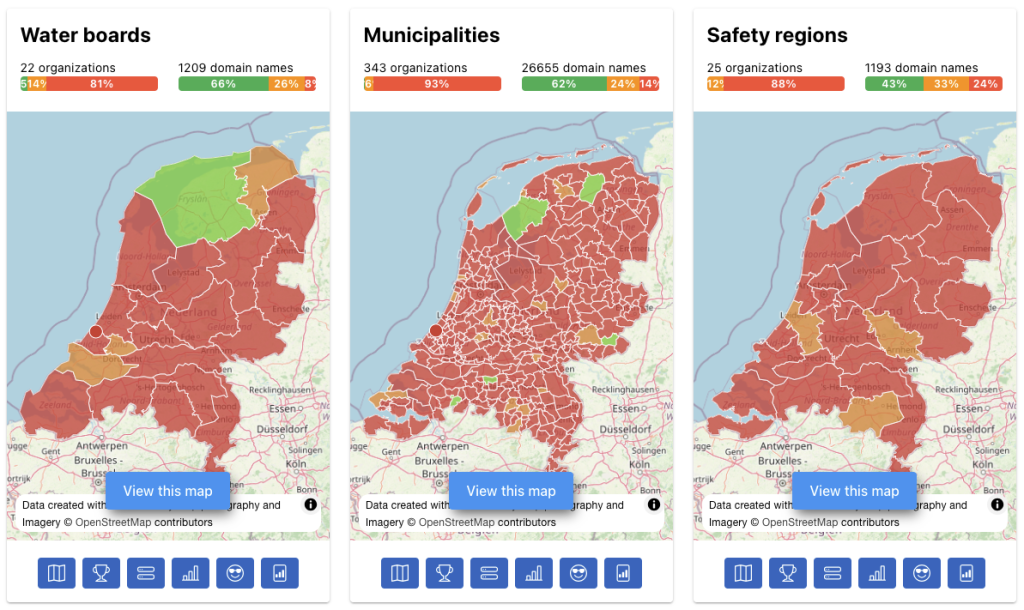
The screenshot below is taken from our Dutch site: basisbeveiliging.nl. This shows three layers of government. What is striking is that the color on the maps is predominantly red. This is because in the Netherlands we measure not only the main site of an organization but also all sites for projects, for example (new neighborhoods, new highways, campaigns and the like). It can be seen that among municipalities, 62% of the 26,655 addresses of municipalities measured score well.
3: Timeline of perusal, publication, scope
The timeline of publication is as follows:
- Feb. 10, 2026: Email with brief advance notice and link to this text
- Feb. 10, 2026: Start period of inspection of measurements and improvements
- Inspection period Feb 10 – May 10:
- Complete measured governments
- Tightening TLS measurements from internet.nl according to NCSC-NL 2025 guidelines 11
- Possible addition of new measurement and visualization on digital sovereignty
- Only main domains and subdomains governments, no domains for projects
- Change requests can be made, only the official domain will be accepted or replaced. Other requests for additional domains will be held until after this period
- May 10, 2026: Publish findings with research article comparing countries
- Period after May 10, 2026:
- Adding more authorities and sites, possibly also project domains
- Change requests for new domains are accepted
The scope table below lists all of our websites and what information can be found on them. Here you can see that the number of SecurityBaseline organizations is large at over 75,000. The number of related domains is still low at 120,000: this will grow to an average of 10 subdomains per domain.
| Website | Organizations | Extent of internet addresses | Measurements |
|---|---|---|---|
| SecurityBaseline.eu (the new website) | All regional European authorities + CSIRT organizations (76,575) | Main domain + subdomains (120,257) | All 25 metrics: security, privacy and sovereignty |
| Basisbeveiliging.nl | The entire Dutch government, vital, education, healthcare, politics, cybersecurity (11,843) | All domains as far as we can find them (361,688) | All 25 metrics: security, privacy and sovereignty |
| Basisbeveiliging.be (will no longer be needed after May 10) | Regional governments of Belgium (640) | Principal domain + subdomains (5,789) | FTP, DMARC, DKIM, SPF, DNSSEC |
| Basistoegankelijk.nl | The entire Dutch government, vital, education, healthcare, politics, cybersecurity (11,843) | All domains as far as we can find them (361,688) | 94 metrics on website accessibility |
4: Policies of the Internet Cleanup Foundation
SecurityBaseline publishes security measurements in a considered manner. Our considerations are compiled in our code of conduct. We measure daily to weekly.
SecurityBaseline works according to the following process:
Exactly which domains of organizations are measured is stated in the domain policy. All measurements performed on these domains are bundled in the measurement policy. Because it is impossible to treat all decisions in IT infrastructure the same way, organizations can declare exceptions. This is called “comply or explain” or “comply or explain.” Many of these declarations are automatically added by automated exceptions to the measurement policy. A good declaration meets a number of requirements.
Exactly what is and is not published is described in the publication policy. The scans performed point back to SecurityBaseline as clearly as possible, where possible directly to the scaninfo page (English only). All measurements and publications are subject to this disclaimer (English only).
5: Accessibility
The Internet Cleanup Foundation can be reached through two avenues:
1: Email to info@internetcleanup.foundation. We will convert emails in foreign languages to Dutch or English. Some nuance may be lost as a result. All mail is read, but it can sometimes take several weeks before we find time to respond.
2: Discord: Visit our discord channel at https://discord.gg/FzadeDrptx ask for Elger, Johan or Wouter. There is also a support channel there where various topics are covered.
6: How did the maps and announcements come about
The maps are based on public data from Open Street Map (areas and names of governments), combined with public data from Wikidata (addresses of websites). A list of organizations and locations was manually collected for the CSIRT layer. A total of 90 maps were compiled. All European countries that have signed the European Economic Area treaty are measured along with Switzerland. We include Switzerland because it is one of the few countries that makes all their Internet domains available through open data, which is progressive.
We intentionally made the main government website part of the CSIRT. Of course, this is not how responsibility is formally invested. We see this more as a social responsibility. We hope that through this means the main government website will be better secured should the need arise.
Because of the 24 languages spoken in Europe, the main pages of this website and of SecurityBaseline.eu have been translated into all of these languages. The translation was done by DeepL unless the language was not available (e.g. Maltese and Icelandic). Translating websites on this scale is proving pricey. We are proud that most of all the text on the site is available in most European languages, including Irish and Greek, although there are sometimes errors in the translations.
The pre-announcement to governments and CSIRT organizations was done via emails in the official languages of the member state. This pre-announcement was sent to all e-mail addresses of local governments and CSIRT organizations as far as they were findable. Some of this came from Wikidata, some of it was automatically collected and filtered with self-written software. In total, tens of thousands of emails were sent. Emails are sent once to avoid inconvenience. We expect that governments talk to each other, and that the lines of communication between the CSIRT and local governments are good. Thus, should we have forgotten or be unable to reach an organization, this existing social network serves as a backstop.
With 90 new maps and many thousands of authorities, there is a good chance that we may be wrong at times. We apologize for the inconvenience. We are taking the period of perusal to continue getting the maps and information on the sites right.
7: How does this work out financially?
We are the Internet Cleanup Foundation from the Netherlands. We are a small team of three people trying to make the world a better place with a lot of knowledge and a small budget. Contact information and details of our foundation can be found on the“About Us” page.
This project is done on our own initiative, with our own resources and in our own time. No payment or amount is required to use our findings or reports. There are also no payment walls for viewing information or its reuse by others. All of our findings are available as open data.
So we do this initiative from within ourselves. But our daily activities are financially supported by the SIDN Fund, the Center for Information Security and Privacy Protection, the State Inspectorate for Digital Infrastructure, the Dutch government and more than 30 participating organizations of our foundation, among others. We receive technical resources sponsored from CoBytes, Procolix, SURF, Sentry, Hack42 and GitLab.
Other income we derive from:
- Research assignments,
- Develop new measurements and platforms,
- Participant contributions from participants to our foundation,
- Performing measurements of sectors upon request.
It is possible to sponsor or support us from a government, as long as our independent position is guaranteed. Please contact elger@internetcleanup.foundation for this. For all other questions: use the addresses in the Reachability section.
It is possible to become a participant of our foundation. We have intentionally not yet made this option available on SecurityBaseline.eu because this may be seen as if we are a commercial enterprise. This will become available later with sufficient clarification. For early participation, please contact elger@internetcleanup.foundation.
8: More about us
Contact information and details of our foundation can be found on the“About Us” page.
